Hey everybody!
Isn’t May a merry month? And for our first release of challenges for May, we have four webapp challenges that range in difficulty from fairly basic to OMG! Looks like a good time to make sure your copy of Burp Suite is up to date. 😉
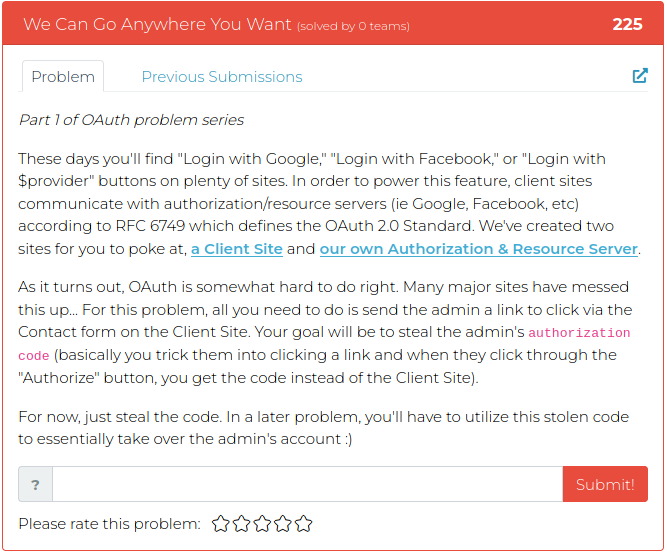
For screenshots and descriptions of this week’s additions, see below.
Good luck and have fun!
The Cyber Range Team
P.S. If you’re not already signed up for the BHIS Antisyphon Cyber Range, the following page has screenshots, info, and, of course, a link where you can sign up and join in the fun: