Hey everybody!
This week’s challenges are comparatively easy, and they cover everything from binary exploits to recon. In that, they are kind of like potpourri. They are light and varied and guaranteed to brighten up the room. 🌼
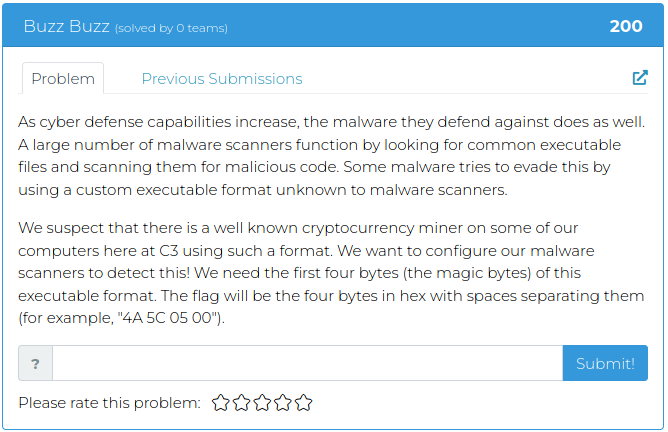
For screenshots and descriptions of this week’s additions, see below.
Good luck and have fun!
The Cyber Range Team
P.S. If you’re not already signed up for the BHIS Antisyphon Cyber Range, the following page has screenshots, info, and, of course, a link where you can sign up and join in the fun: